API protection
Remediate and patch at your own pace. Avoid project delays and achieve operational serenity. We create a secure environment where existing vulnerabilities have no impact on your day-to-day work.
Gartner predicts that application programming interface (API) attacks will become the most-frequent attack vector, causing data breaches for enterprise web applications.
The cold, hard truth is this: cyberattackers work around the clock. They’re flexible, adaptable, and consistently grow in number and sophistication.
And the way most organizations are thinking about and deploying security is no longer enough.
We have a better way. A simpler way! The Cloudpurge ‘click with no fear’ way.
In a world where cybersecurity responses often fall behind attacks, leaving cyber security teams firefighting and exhausted, Cloudpurge offers a proactive solution.
Cloudpurge implement true zero-trust, isolating and controlling every interaction.
Think of Cloudpurge as the invisible, invincible zone that shields your systems from modern-day cyber threats.
How does it work?

CLOUDPURGE PROTECTS THE MOST TARGETED ATTACK VECTORS

Remediate and patch at your own pace. Avoid project delays and achieve operational serenity. We create a secure environment where existing vulnerabilities have no impact on your day-to-day work.



Block bot traffic without interrupting their user experience. No direct Access that would traditionally facilitate a breach.

Traditional cybersecurity solutions are complicated and expensive to run and operate. Cloudpurge is the opposite. It's cost-efficient, simple and easy to deploy, and even helps you to free up your engineering resources. By isolating every interaction, it prevents threat actors from accessing and harming our system.
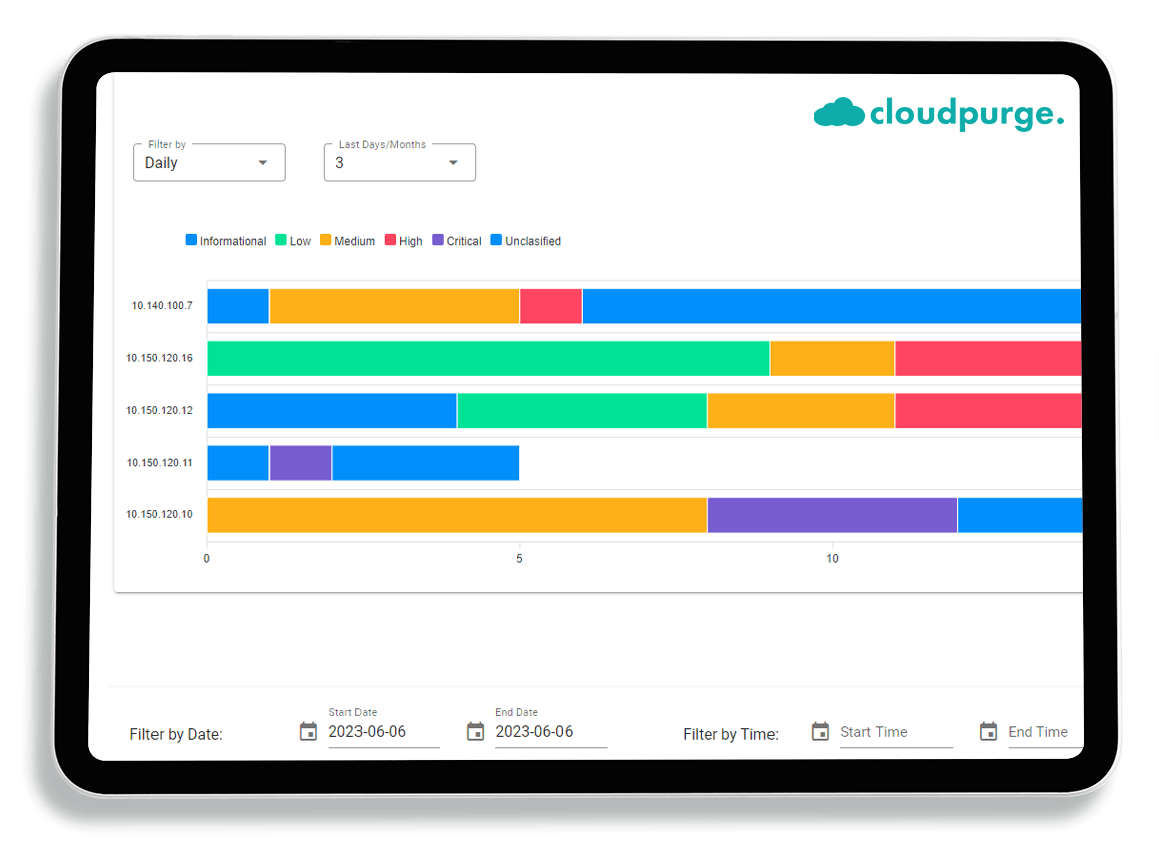
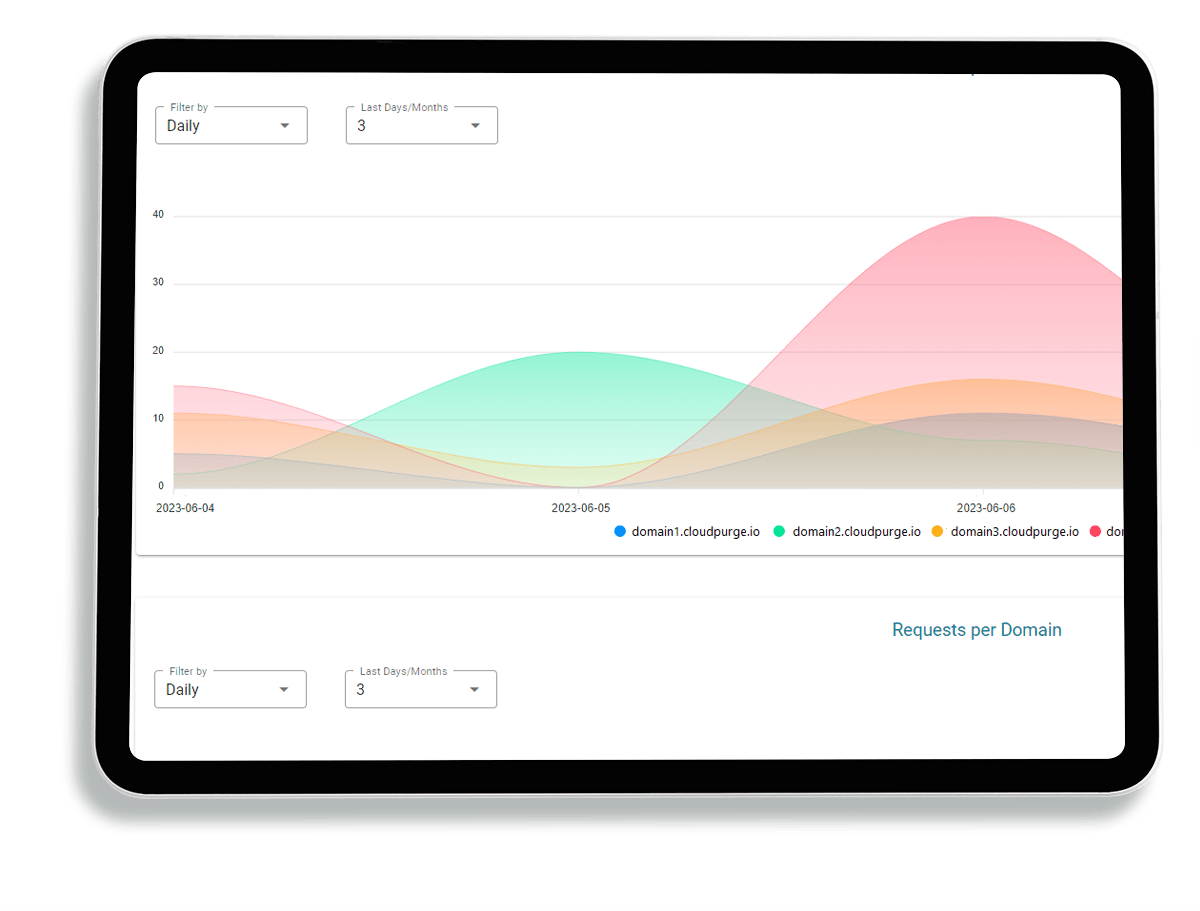
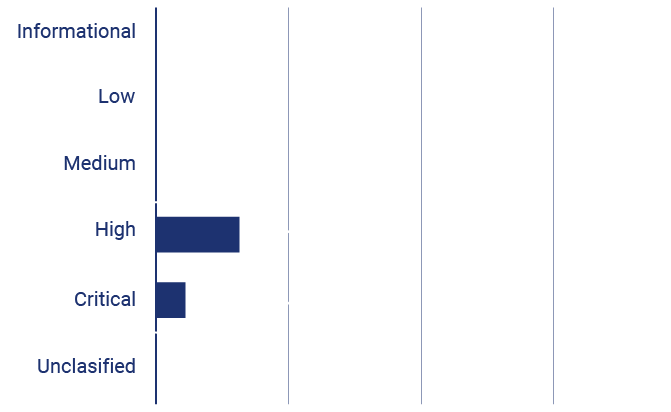
Book a consultationCloudpurge intercepts, isolates and logs every interaction with your system in a single dashboard so you can inspect incoming traffic and assess harmful intent.
That way you can implement a second layer of protection and block real threat sources without spreading your engineers too thin.
Book a consultation